本节书摘来自异步社区《Nmap渗透测试指南》一书中的第1章1.8节全面扫描,作者 商广明,更多章节内容可以访问云栖社区“异步社区”公众号查看。
1.8 全面扫描
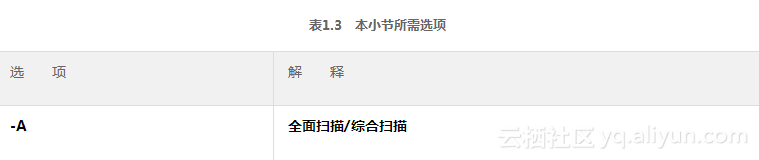
Nmap全面扫描的选项是-A,它可以全面扫描指定IP或域名的所有端口及其目标系统信息等,这需要花费点时间等待Nmap的扫描。
root@Wing:~# nmap -A 192.168.126.131
Starting Nmap 6.40 ( http://nmap.org ) at 2014-06-12 15:43 CST
Nmap scan report for 192.168.126.131
Host is up (0.00040s latency).
Not shown: 977 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4 #FTP服务商是vsftpd,版本是2.3.4
|_ftp-anon: Anonymous FTP login allowed (FTP code 230) #允许匿名登录
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0) #SSH供应商是OpenSSH 版本是4.7
| ssh-hostkey: 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA)#秘钥
|_2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA)
23/tcp open telnet Linux telnetd #Telnet服务
25/tcp open smtp Postfix smtpd #Smtp服务
|_smtp-commands: metasploitable.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN,
| ssl-cert: Subject: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/ stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2010-03-17T14:07:45+00:00
|_Not valid after: 2010-04-16T14:07:45+00:00
|_ssl-date: 2014-06-10T10:00:54+00:00; -1d21h42m30s from local time.
53/tcp open domain ISC BIND 9.4.2 #DNS服务端口
| dns-nsid:
|_ bind.version: 9.4.2
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) DAV/2) #HTTP服务
|_http-methods: No Allow or Public header in OPTIONS response (status code 200)
|_http-title: Metasploitable2 - Linux
111/tcp open rpcbind 2 (RPC #100000) #RPC服务
| rpcinfo: #RPC服务详细信息
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100003 2,3,4 2049/tcp nfs
| 100003 2,3,4 2049/udp nfs
| 100005 1,2,3 40529/tcp mountd
| 100005 1,2,3 43983/udp mountd
| 100021 1,3,4 41255/tcp nlockmgr
| 100021 1,3,4 55723/udp nlockmgr
| 100024 1 35526/tcp status
|_ 100024 1 50609/udp status
139/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP) #Samba版本为5.X
445/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP) #Samba版本为5.X
512/tcp open exec netkit-rsh rexecd
513/tcp open login?
514/tcp open tcpwrapped
1099/tcp open rmiregistry GNU Classpath grmiregistry
|_rmi-dumpregistry: Registry listing failed (No return data received from server)
1524/tcp open shell Metasploitable root shell
2049/tcp open nfs 2-4 (RPC #100003)
2121/tcp open ftp ProFTPD 1.3.1
3306/tcp open mysql MySQL 5.0.51a-3ubuntu5
| mysql-info: Protocol: 10
| Version: 5.0.51a-3ubuntu5
| Thread ID: 21
| Some Capabilities: Connect with DB, Compress, SSL, Transactions, Secure Connection
| Status: Autocommit
|_Salt: fRHP:oB9:Tvy|$:6@}uU
5432/tcp open postgresql PostgreSQL DB 8.3.0 - 8.3.7
5900/tcp open vnc VNC (protocol 3.3)
| vnc-info:
| Protocol version: 3.3
| Security types:
|_ Unknown security type (33554432)
6000/tcp open X11 (access denied)
6667/tcp open irc Unreal ircd
| irc-info:
| server: irc.Metasploitable.LAN
| version: Unreal3.2.8.1. irc.Metasploitable.LAN
| servers: 1
| users: 1
| lservers: 0
| lusers: 1
| uptime: 0 days, 23:24:39
| source host: A5B014C0.D9689365.FFFA6D49.IP
|_ source ident: nmap
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
|_ajp-methods: Failed to get a valid response for the OPTION request
8180/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-favicon: Apache Tomcat
|_http-methods: No Allow or Public header in OPTIONS response (status code 200)
|_http-title: Apache Tomcat/5.5
MAC Address: 00:0C:29:E0:2E:76 (VMware) #目标主机MAC地址
Device type: general purpose #设备类型
Running: Linux 2.6.X #目标主机操作系统
OS CPE: cpe:/o:linux:linux_kernel:2.6 #目标主机中央处理单元
OS details: Linux 2.6.9 - 2.6.33 #目标主机详细资料
Network Distance: 1 hop #网络距离
Service Info: Hosts: metasploitable.localdomain, localhost, irc.Metasploitable.LAN; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_nbstat: NetBIOS name: METASPLOITABLE, NetBIOS user: , NetBIOS MAC:
| smb-os-discovery: #SMB系统发现
| OS: Unix (Samba 3.0.20-Debian) #操作系统为Unix,Samba版本为2.0.20
| NetBIOS computer name: #NetBIOS计算机名称
| Workgroup: WORKGROUP #所在工作组
|_ System time: 2015-06-10T06:00:51-04:00 #系统时间
TRACEROUTE
HOP RTT ADDRESS
1 0.41 ms 192.168.126.131
OS and Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 26.21 seconds
root@Wing:~#
全面扫描又称作综合扫描,是一种完整扫描目标信息的扫描方式。





