说到CA(CS)服务相信很多人运维人员都比较熟悉的一个服务,CA(Certificate Authority),CS(Certificate Service)不仅在windows服务存在,同样也在linux下存在,主要目的是提高安全性的,CA 也拥有一个证书(内含公钥和私钥)。网上的公众用户通过验证 CA 的签字从而信任 CA ,任何人都可以得到 CA 的证书(含公钥),用以验证它所签发的证书。如果用户想得到一份属于自己的证书,他应先向 CA 提出申请。在 CA 判明申请者的身份后,便为他分配一个公钥,并且 CA 将该公钥与申请者的身份信息绑在一起,并为之签字后,便形成证书发给申请者。如果一个用户想鉴别另一个证书的真伪,他就用 CA 的公钥对那个证书上的签字进行验证,一旦验证通过,该证书就被认为是有效的。证书实际是由证书签证机关(CA)签发的对用户的公钥的认证。证书的内容包括:电子签证机关的信息、公钥用户信息、公钥、权威机构的签字和有效期等等。目前,证书的格式和验证方法普遍遵循X.509 国际标准。证书的工作原理是:加密和解密;加密就是将文字转换成不能直接阅读的形式(即密文)的过程称为加密。即把我们平时看到的“http”加密成“https”来传输,这样保证了信息在传输的过程中不被窃听;而解密就是:我们将密文转换成能够直接阅读的文字(即明文)的过程称为解密。具体就不多说了,如果有不明白的可以在网上找找相关的文档查阅,接下来说说我的环境;
公司环境不是太复杂,多个站点部署了多个DC来提高访问效率,在北京的站点中有三台DC,其中有一台DC上运行着ADCS服务,对于CA的部署架构微软建议独立运行,不建议和ADDS在在同一台服务器上运行,近期由于公司做了AD的健康检查, 检测出运行CA服务的DC数据库损坏,导致整个环境非常危险,之前的想法是直接降级DC只保存CA服务运行,可在实施的时候发现在卸载ADDS服务的时候提示运行这个CA服务,必须在卸载CS服务后才能对DC降级,所以被迫无奈对整个CA服务进行迁移,然后对DC降级,最后对整个CA的迁移做了一个笔记,以致给大家分享出来。需要注意的是,此次做迁移的时候我的CA旧服务名称和CA新服务器名称不一样,所以在迁移的时候我们需要注意一下。具体见下:
Active Directory Certificate Services Migration Guide
http://technet.microsoft.com/en-us/library/ee126170(v=ws.10).aspx
Here is a detailed steps that I summarized, please check:
https://technet.microsoft.com/zh-cn/library/9aa53be9-0497-49fa-9ff6-09b72cb69444(v=ws.10)#BKMK_AddCA
https://technet.microsoft.com/zh-cn/library/ee126170(v=ws.10).aspx
===Enterprise Root CA Migration Steps===
1. First we need to do a full CA database backup using the following command:
CERTUTIL -f -p <password> -backup <backup path like C:\CABackup>
Note: Please remember that <password> you specify in the command above, it will be used when install the CA later.
备份完成
或者使用手动的方式备份
使用“证书颁发机构”管理单元备份 CA 数据库和私钥
-
选择备份位置并附加媒体(如有必要)。
-
登录到源 CA。
-
打开“证书颁发机构”管理单元。
-
右键单击包含 CA 名称的节点,指向“所有任务”,然后单击“备份 CA”。
-
在 CA 备份向导的“欢迎”页上,单击“下一步”。
-
在“要备份的项目”页上,选中“私钥和 CA 证书”以及“证书数据库和证书数据库日志”复选框,指定备份位置,然后单击“下一步”。
-
在“选择密码”页上,键入用于保护 CA 私钥的密码,并单击“下一步”。
备份完成
-
在“正在完成备份向导”页上,单击“完成”。
-
备份完成后,验证所指定的位置中的以下文件:
-
包含 CA 证书和私钥的 CA 名称.p12
-
包含文件 certbkxp.dat、edb#####.log 和 CA 名称.edb 的 Database 文件夹
打开命令提示符窗口,并键入 net stop certsvc 以停止“Active Directory 证书服务”服务
2. Back The CA service registry key:
备份 CA 注册表设置
REG export HKLM\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration C:\CABackup\RegBak.reg
使用 Regedit.exe 备份 CA 注册表设置
-
单击“开始”,指向“运行”,并键入 regedit 以打开注册表编辑器。
-
在 HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc 中,右键单击“Configuration”,然后单击“导出”。
-
指定位置和文件名,然后单击“保存”。这将创建一个包含源 CA 中的 CA 配置数据的注册表文件。
-
将该注册表文件复制到可从目标服务器中访问的位置;例如,共享文件夹或可移动媒体。
备份完成
或者使用以下方式备份
使用 Reg.exe 备份 CA 注册表设置
-
打开命令提示符窗口。
-
键入 reg export HKLM\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration <输出文件.reg>,并按 Enter。
-
将该注册表文件复制到可从目标服务器中访问的位置;例如,共享文件夹或可移动媒体。
3. Publishing a CRL with an extended validity period:
a. In the CA console, right click on the Revoked Certificates->All Tasks->Publish->New CRL
b. Then you will have additional week CRL(default value is 1 week) for the current certificate to use during the migration.
c. <Manually publish the certificate revocation list>
http://technet.microsoft.com/en-us/library/cc778151(WS.10).aspx
我们看见rpc服务器不可用,我们需要net start certsvc 启动后就正常了
windows\system32\certsrv\CertEnroll
4. Backup CAPolicy.inf: (因为没有定义,所以我们忽略该步骤)
If your source CA is using a custom CAPolicy.inf file, you should copy the file to the same location on the destination server as the source CA backup files. The CAPolicy.inf file is located in the %SystemRoot% directory, which is usually C:\Windows.
5. Backup CA templates list: (也可以忽略该步骤)
a. Open a Command Prompt window.
b. Run
certutil.exe -catemplates > catemplates.txt
then Verify that the catemplates.txt file contains the templates list.
6. Remove the CA service on the server, use the Remove Roles Wizard in Server Manager.
提示我们需要先卸载WEB服务iis才能卸载
继续卸载AD证书服务
7. Copy the CA backup folder to the new CA server.
8. Import the CA certificates:
a. Start the Certificates MMC snap-in for the local computer account.
b. In the console tree, double-click Certificates (Local Computer), and click Personal.
c. On the Action menu, click All Tasks, and then click Import to open the Certificate Import Wizard. Click Next.
d. Locate the <CAName>.p12 file created by the CA certificate and private key backup on the source CA, and click Open.
e. Type the password in the first step, and click OK.
f. Click Place all certificates in the following store.
g. Verify Personal is displayed in Certificate store. If it is not, click Browse, click Personal, and click OK.
9. Adding the CA role service by using Server Manager on the new installed server:
a. Start Server Manager.
b. In the console tree, click Roles.
c. On the Action menu, click Add Roles.
d. If the Before you Begin page appears, click Next.
e. On the Select Server Roles page, select the Active Directory Certificate Services check box, and click Next.
f. On the Introduction to AD CS page, click Next.
g. On the Role Services page, click the Certification Authority check box, and click Next.
Note: If you plan to install other role services on the destination server, you should complete the CA installation first, and then install other role services separately. Installation procedures for other AD CS role services are not described in this guide.
8. On the Specify Setup Type page, specify either Enterprise or Standalone, to match the source CA, and click Next.
9. On the Specify CA Type page, specify either Root CA or Subordinate CA, to match the source CA, and click Next.
10.On the Set Up Private Key page, select Use existing private key and Select a certificate and use its associated private key.
11.In the Certificates list, click the imported CA certificate, and then click Next.
12.On the Configure Certificate Database page, specify the locations for the CA database and log files.
13.On the Confirm Installation Selections page, review the messages, and then click Install.
10.Restore the CA database from the backup:
a. Use CA administrator to log on to the destination server by using an account that is a CA administrator.
b. Start the Certification Authority snap-in.
c. Right-click the node with the CA name, point to All Tasks, and then click Restore CA. If prompted, click OK to stop the CA service.
d. On the Welcome page, click Next.
e. On the Items to Restore page, select Certificate database and certificate database log.
f. Click Browse, and locate the Database directory that contains the CA database files created during the CA database backup.
NOTE: Do not select the Database directory. Select its parent directory.
7. Type the password that you used to back up the CA database on the source CA.
8. Click Finish, and then click Yes to restart the CA service
https://technet.microsoft.com/zh-cn/library/ee126140(v=ws.10)#BKMK_RestoreReg
11.Since we are migrating the CA from one server to another using the different server name, before we import the registry exported from the old server, we first use text editor to change the CA servername from old one to the new one:
net stop certsvc
a. Right-click the .reg file created by exporting the settings from the source CA.
b. Click Edit to open the file in a text editor.
c. If the target CA's computer name is different from the source CA's computer name, search the file for the host name of the source CA computer. For each instance of the host name found, ensure that it is the appropriate value for the target environment. Change the host name, if necessary. Update the CAServerName value.
Do not change Active value within the Configuration key and the CommonName value within the CAName key. The CA name must not be changed as part of the migration.
This means the new target CA must have the old CA's name, even if part of that name is the old CA's host name.
4. Check any registry values that indicate local file paths, such as the following, to ensure drive letter names and paths are correct for the target CA. If there is a mismatch between the source and the target CA, either update the values in the file or remove them from the file so that the default settings are preserved on the target CA.
5. These storage location settings are elected during CA setup. They exist under the Configuration registry key:
a. DBDirectory
b. DBLogDirectory
c. DBSystemDirectory
d. DBTempDirectory
6. The following settings under the Configuration\{CA Name} registry key contain, in their default values, a local path. (Alternatively, you can update these values after importing them by using the Certification Authority snap-in. The values are located on the CA properties Extensions tab.)
a. CACertPublicationURLs
b. CRLPublicationURLs
7. Any values not listed can retain the value data installed by default with the target CA. You can remove any registry values that you do not want to import into the target CA. Once the text file is edited, it can be imported into the target CA. By importing the source server registry settings backup into the destination server, the source CA configuration is migrated to the destination server.
12.After modifying the registry, we can import it into the new CA server.(以下操作均为确认操作,可以忽略)
a. Stop the Certificate service: net stop certsvc.
b. Locate the registry file that you just modified in the backup folder, and then double-click it to import the registry settings.
c. Open Regedit, in the console tree, locate the key HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\CertSvc\Configuration, and click Configuration.
d. In the details pane, double-click DBSessionCount.
e. Click Hexadecimal. In Value data, type 64, and then click OK.
f. Verify the locations specified in the following settings are correct for your destination server, and change them as needed to indicate the location of the CA database and log files.
a. DBDirectory
b. DBLogDirectory
c. DBSystemDirectory
d. DBTempDirectory
13.Restore the Certificate Template list:
a. Open a command prompt window.
b. Run
certutil -setcatemplates +<templatelist>
NOTE: Replace <templatelist> with a comma-separated list of the template names that are listed in the catemplates.txt file created during Step 6.
For example,
certutil -setcatemplates +Administrator,User,DomainController
14.Start the CA service. After CA service startup, please do the following things to mapping the CDP to old location for existing certifications:
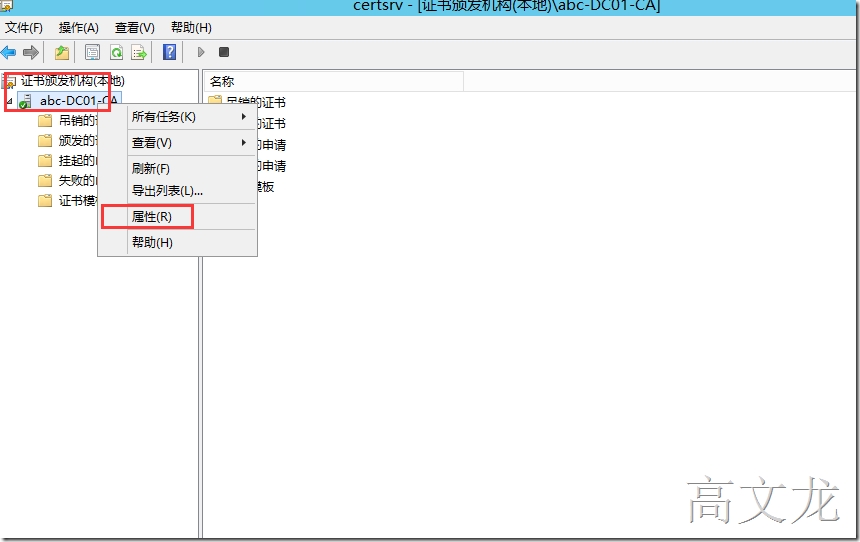
a. Open CA console, right click on the CA name and Properties.
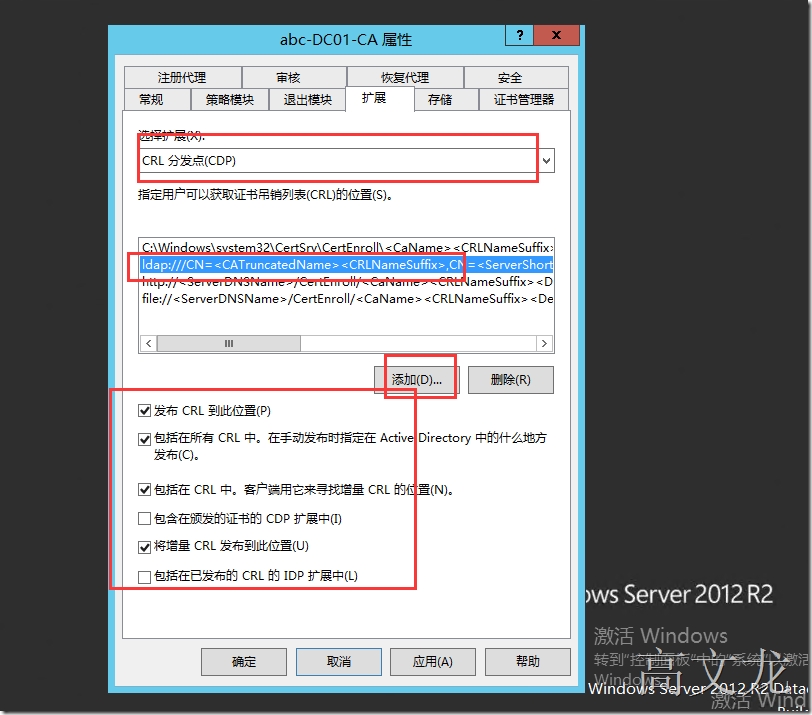
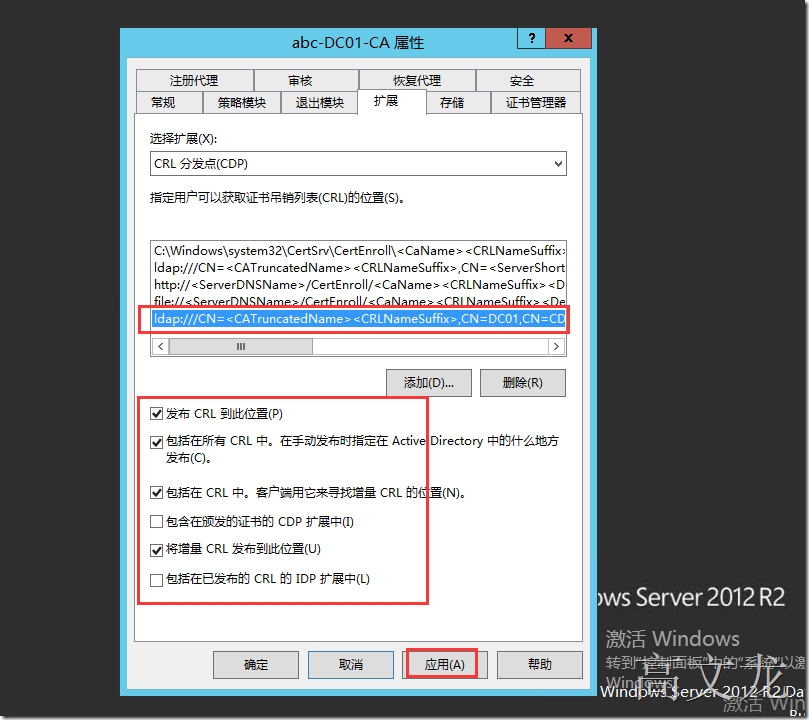
b. In the Extensions tab, check the CDP, add the old CDP into the list:
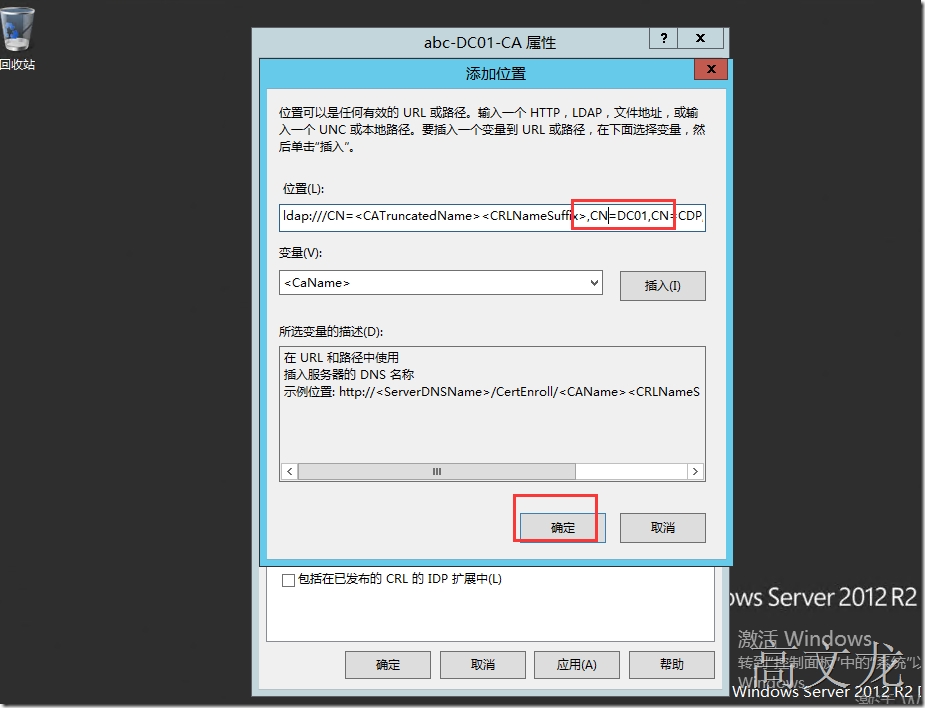
添加以下内容,但是需要修改OLDservername
ldap:///CN=<CATruncatedName><CRLNameSuffix>,CN=OldServerName,CN=CDP,CN=Public Key Services,CN=Services,<ConfigurationContainer><CDPObjectClass>
Check all the options below:
1. Publish CRLs to this location
2. Include in all CRLs. Specifies where to publish in the Active Directory when publishing manually.
3. Include in CRLs. Clients use this to find Delta CRL locations.
4. Publish Delta CRLs to this location
修改旧的Caname
注意勾选以下内容
提示会重启CA服务
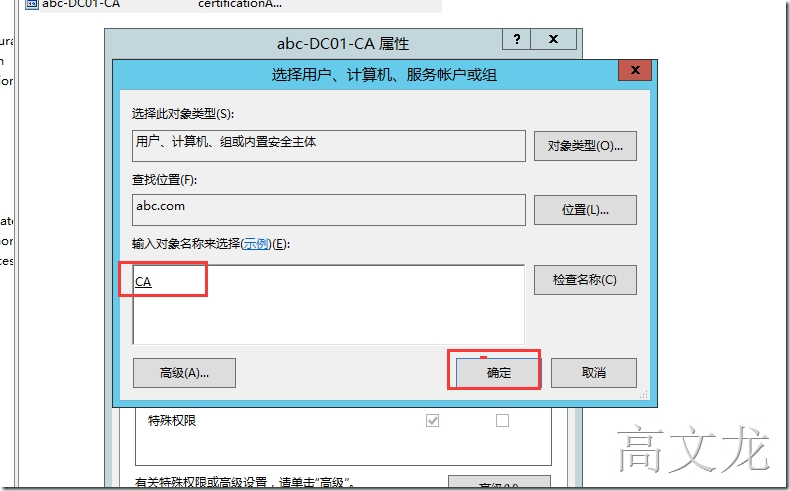
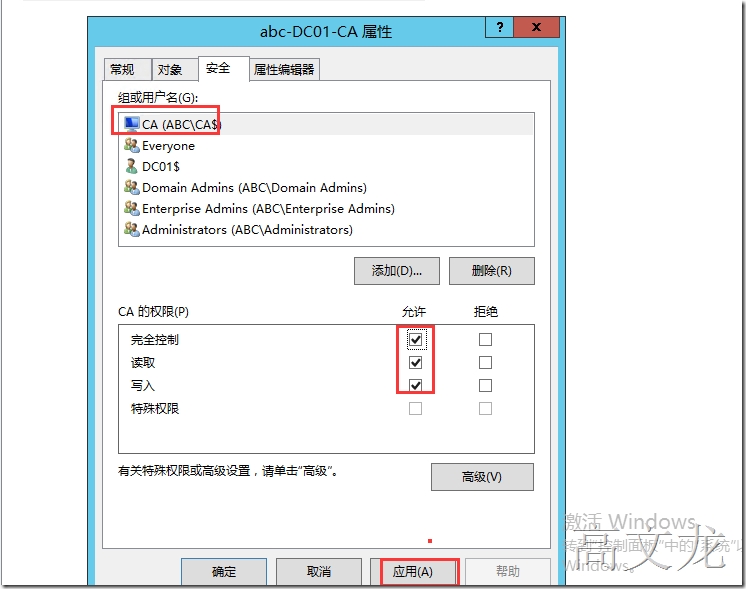
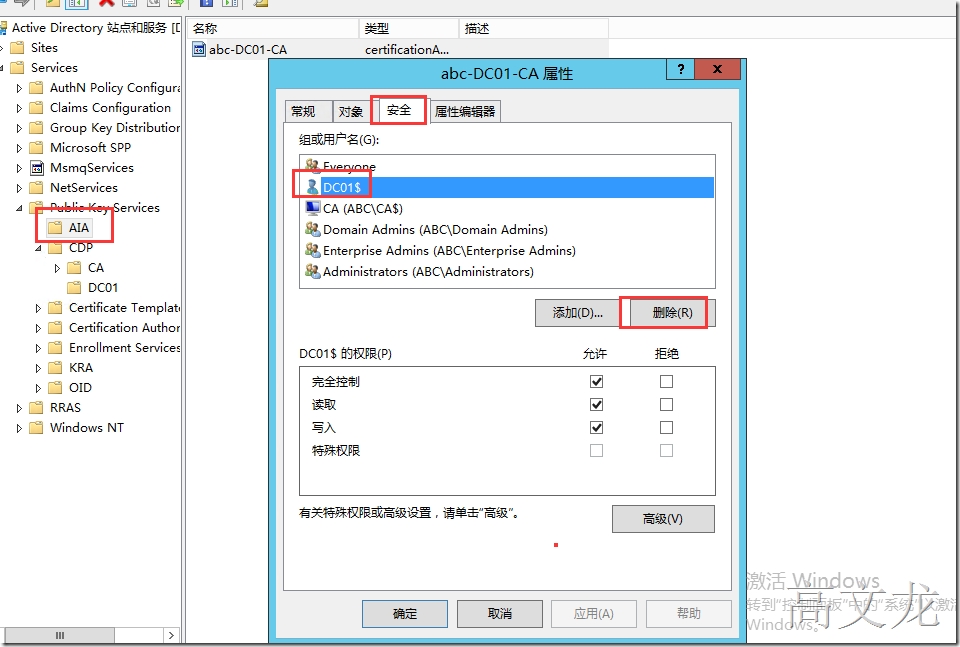
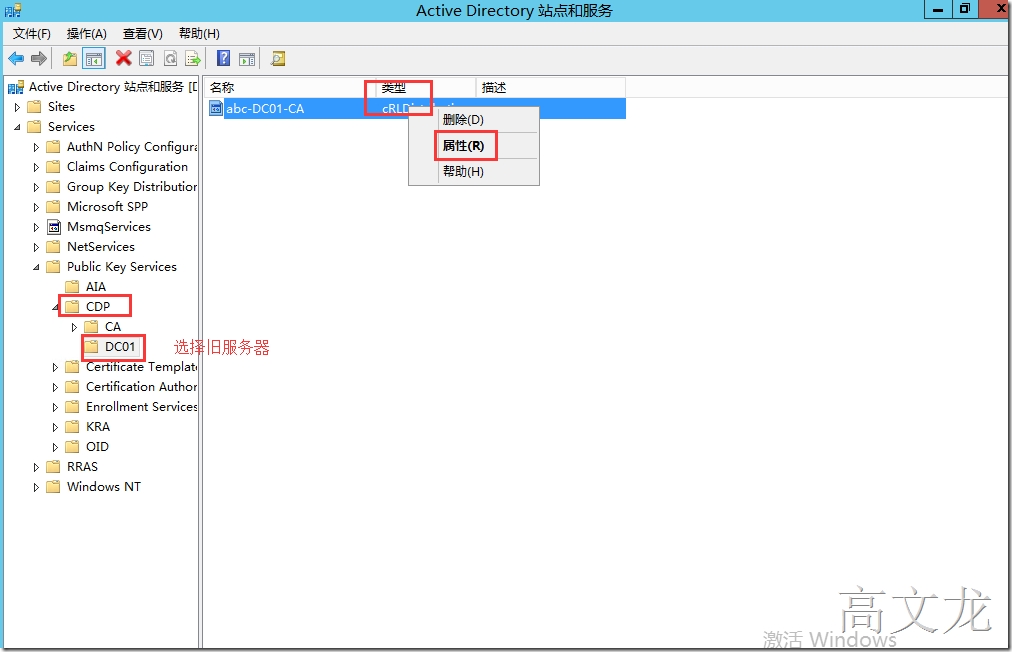
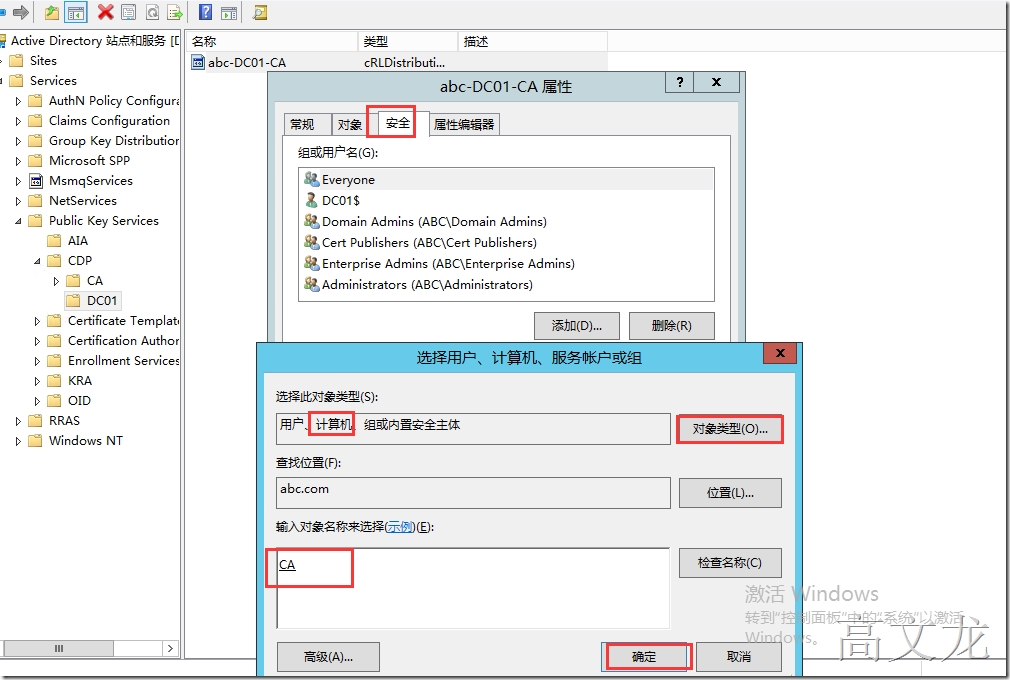
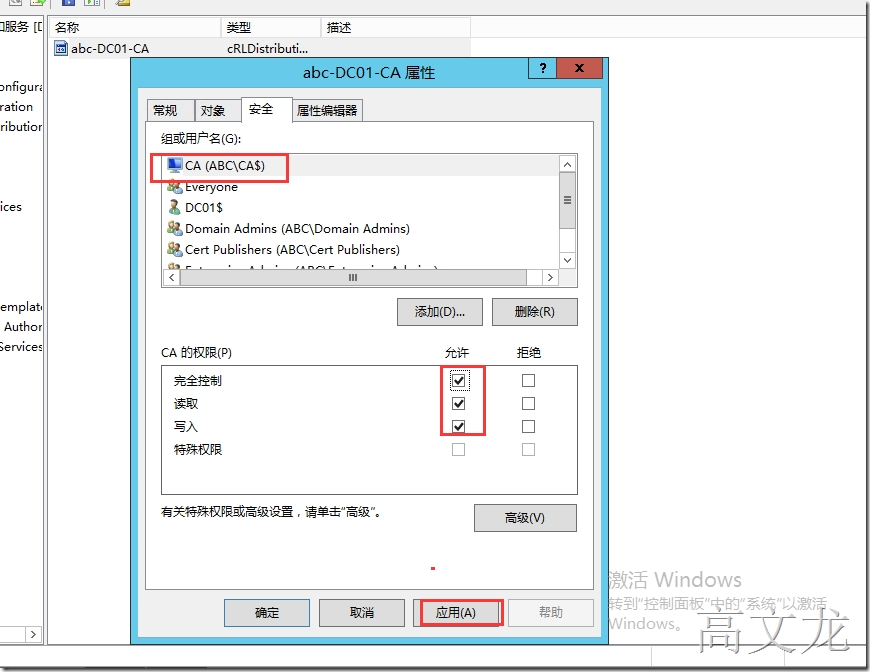
15.Assign permission on the AIA and CDP containers:
a. Log on as a member of the Enterprise Admins group to a computer on which the Active Directory Sites and Services snap-in is installed.
b. Click Start, point to Run, type dssite.msc, and then click OK.
c. In the console tree, click the top node.
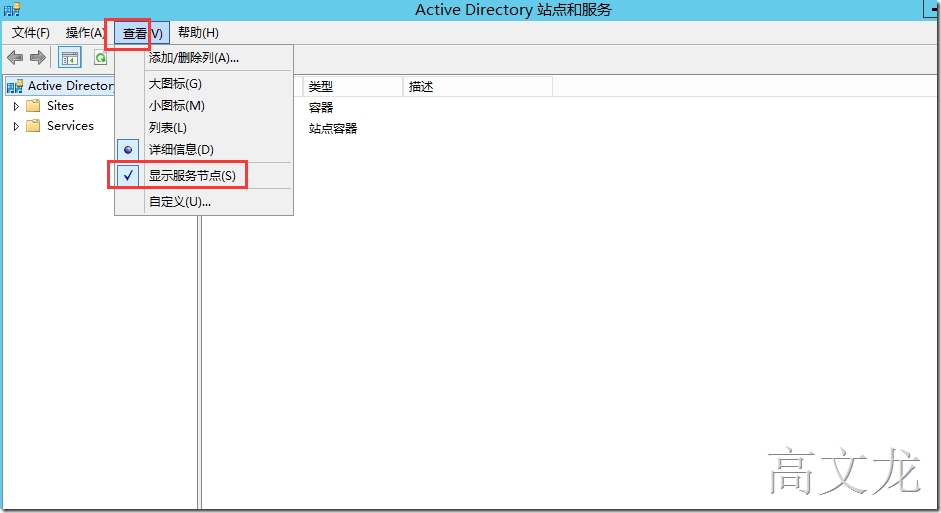
d. On the View menu, click Show services node.
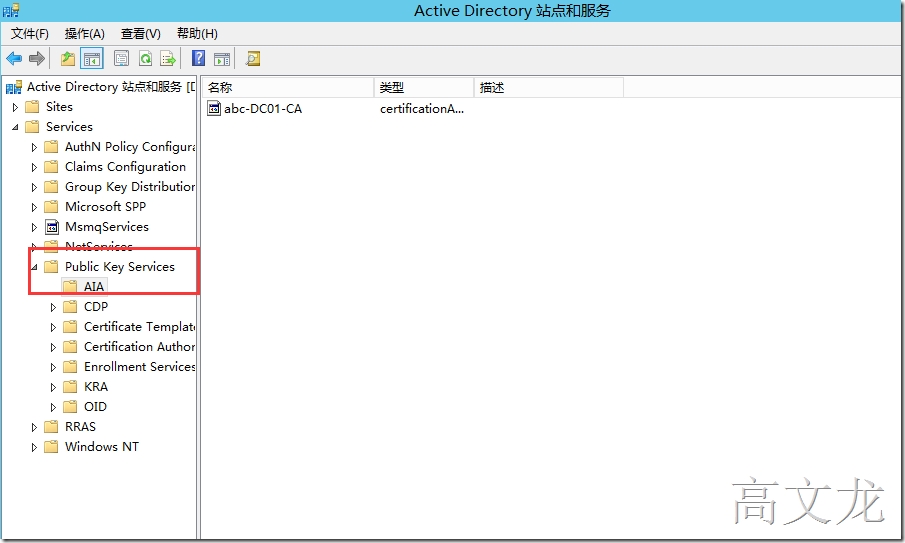
e. In the console tree, expand Services, expand Public Key Services, and then click AIA.
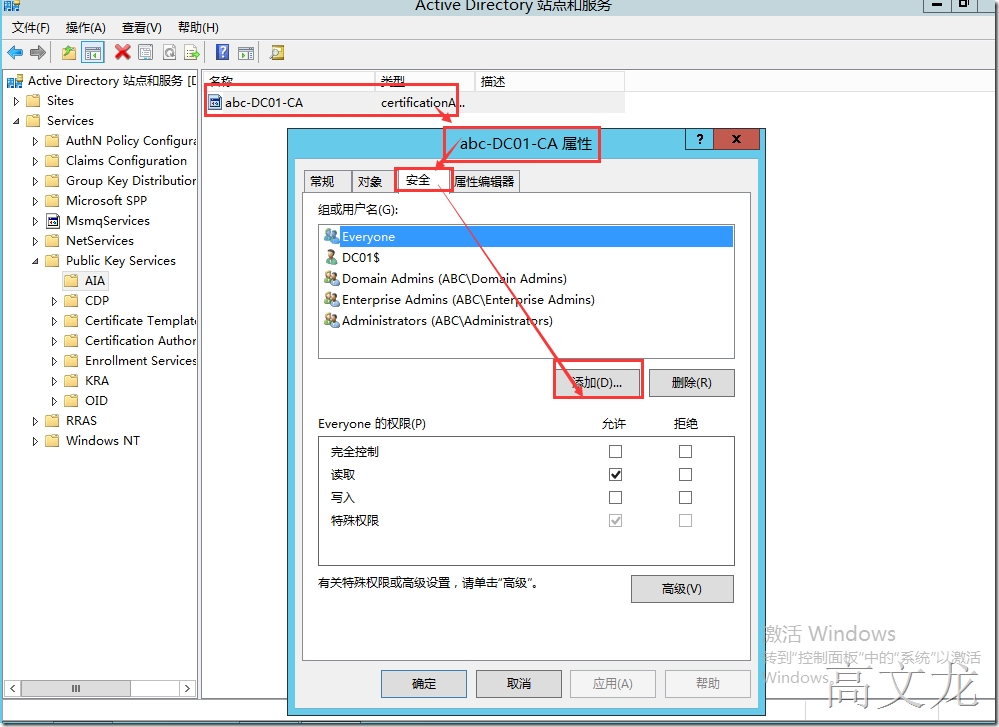
f. In the details pane, right-click the name of the CA, and then click Properties.
g. Click the Security tab, and then click Add.
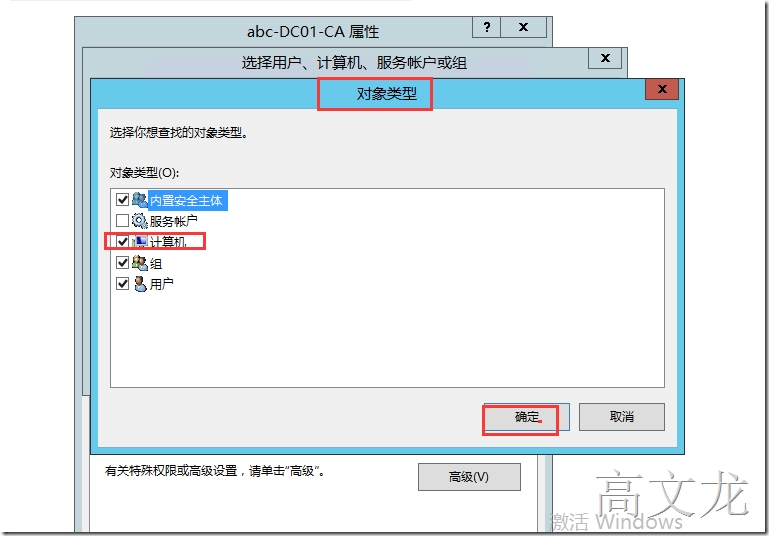
h. Click Object Types, click Computers, and then click OK.
i. Type the name of the NewServer$, and click OK.
j. In the Allow column, click Full Control, and click Apply.
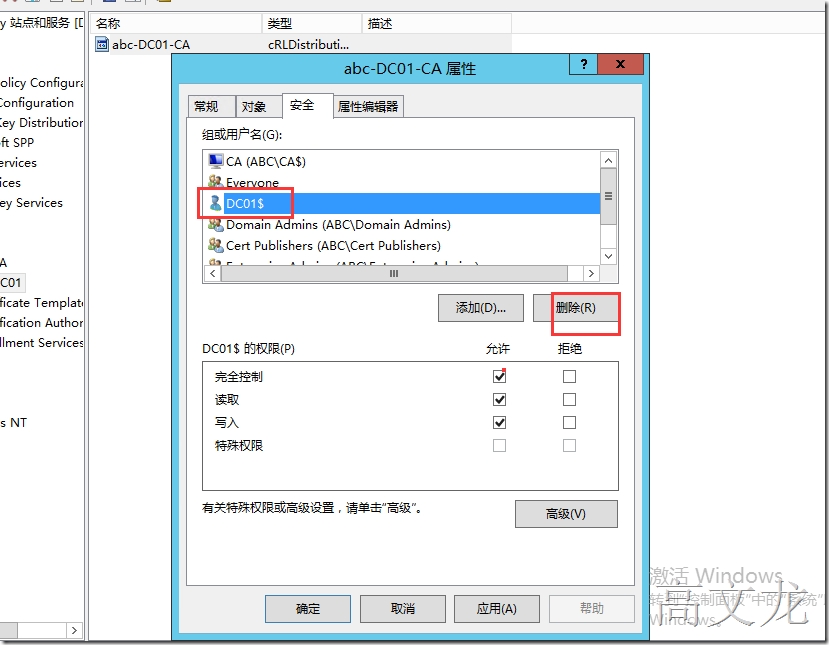
k. If the source server object is displayed in Group or user names, click the name of the source server, then click Remove, and then click OK.
l. In the console tree, expand CDP, and then click the name of the old server.
m. In the details pane, right-click the cRLDistributionPoint item at the top of the list, and then click Properties.
n. Click the Security tab, and then click Add.
o. Click Object Types, click Computers, and then click OK.
p. Type the name of the NewServer$, and click OK.
q. In the Allow column, click Full Control, and click Apply.
r. If the old server object is displayed in Group or user names, click the name of the source server, then click Remove, and then click OK.
s. Repeat steps for each cRLDistributionPoint item in old server CDP.
After all the steps above, every time the new CA publish CRL, it will publish to both its own CDP and old CDP in AD. So the new issued certificates can find the new CDP to check the CRL, and the existing certificates will still be able to find the old CDP to check latest CRL.
最后我们只需要通过申请办法证书测试即可;同时运行
pkiview.msc查看状态
本文转自 高文龙 51CTO博客,原文链接:http://blog.51cto.com/gaowenlong/1701013,如需转载请自行联系原作者
![clip_image001[4] clip_image001[4]](http://s3.51cto.com/wyfs02/M02/74/2D/wKiom1YWcVGSz0uNAAKVym3zUtE969.jpg)
![clip_image002[4] clip_image002[4]](http://s3.51cto.com/wyfs02/M00/74/2D/wKiom1YWcVGh-YfaAAGv4ndv0e8963.jpg)
![clip_image003[4] clip_image003[4]](http://s3.51cto.com/wyfs02/M01/74/2D/wKiom1YWcVKxfkQXAAKfVpO-FbM981.jpg)
![clip_image004[4] clip_image004[4]](http://s3.51cto.com/wyfs02/M02/74/2D/wKiom1YWcVLyt9pPAAKPkpLBdU4625.jpg)
![clip_image005[4] clip_image005[4]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcVLDux2kAAG7ujB6fuk776.jpg)
![clip_image006[4] clip_image006[4]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcVKyc92TAAGn0T8b-ys771.jpg)
![clip_image007[4] clip_image007[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcVPBSAfRAASoCLmPItU840.jpg)
![clip_image008[4] clip_image008[4]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcVPRTRn_AATGwgjJGxc514.jpg)
![clip_image009[4] clip_image009[4]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcVPSsqGSAAFzW5LkaCw128.jpg)
![clip_image010[4] clip_image010[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcVOjZGA1AAFZb1rM8IM674.jpg)
![clip_image011[6] clip_image011[6]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcVPQMsitAAIoAMX6pEg791.jpg)
![clip_image012[4] clip_image012[4]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcVShoyNfAAIRrkcccmQ341.jpg)
![clip_image013[4] clip_image013[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcVTzvAyOAAJzV6AOU58923.jpg)
![clip_image014[4] clip_image014[4]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcVSA3MiBAALWuJSjkKg011.jpg)
![clip_image015[4] clip_image015[4]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcVSDheZqAAKTOqJXGEQ548.jpg)
![clip_image015[5] clip_image015[5]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcVTRQ8JzAAKTOqJXGEQ440.jpg)
![clip_image015[6] clip_image015[6]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcVXhXIjCAAKTOqJXGEQ261.jpg)
![clip_image016[4] clip_image016[4]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcVWA1J3wAAJ-sXvAIb0590.jpg)
![clip_image017[4] clip_image017[4]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcVWBVySXAAIigJVz6vM932.jpg)
![clip_image018[4] clip_image018[4]](http://s3.51cto.com/wyfs02/M01/74/2B/wKioL1YWcW3DlIXaAAGMx1xF1Ps370.jpg)
![clip_image019[4] clip_image019[4]](http://s3.51cto.com/wyfs02/M02/74/2B/wKioL1YWcW2RPWJkAAGeolHWJfE262.jpg)
![clip_image020[4] clip_image020[4]](http://s3.51cto.com/wyfs02/M00/74/2B/wKioL1YWcW2DmJTfAAMeN2eOhZU819.jpg)
![clip_image021[4] clip_image021[4]](http://s3.51cto.com/wyfs02/M01/74/2B/wKioL1YWcW2A2bjjAAJ5SFeR14Y661.jpg)
![clip_image022[4] clip_image022[4]](http://s3.51cto.com/wyfs02/M02/74/2B/wKioL1YWcW2yscoGAAKn8DF0s2k754.jpg)
![clip_image023[4] clip_image023[4]](http://s3.51cto.com/wyfs02/M00/74/2B/wKioL1YWcW7g_HU9AAJJZttlGgM175.jpg)
![clip_image024[4] clip_image024[4]](http://s3.51cto.com/wyfs02/M01/74/2B/wKioL1YWcW6zMYAWAAKlOdeGTnc604.jpg)
![clip_image025[4] clip_image025[4]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcVfjWXbWAALo4KfkdI8718.jpg)
![clip_image026[4] clip_image026[4]](http://s3.51cto.com/wyfs02/M00/74/2B/wKioL1YWcW7Sa2SwAANinYGW2jY756.jpg)
![clip_image026[5] clip_image026[5]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcVfjYIV4AANinYGW2jY738.jpg)
![clip_image027[4] clip_image027[4]](http://s3.51cto.com/wyfs02/M01/74/2B/wKioL1YWcW-wrMwOAAMX443NaOE073.jpg)
![clip_image028[4] clip_image028[4]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcVizW6S6AANyHvfsr10969.jpg)
![clip_image029[4] clip_image029[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcXCwlH91AALu7_E649s356.jpg)
![clip_image029[5] clip_image029[5]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcXChYVXsAALu7_E649s099.jpg)
![clip_image030[4] clip_image030[4]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcXCiLhnaAAMr4sUHndo596.jpg)
![clip_image030[5] clip_image030[5]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcXGgATwNAAMr4sUHndo293.jpg)
![clip_image031[4] clip_image031[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcXHhDkmpAAHWSD0nVm8259.jpg)
![clip_image032[4] clip_image032[4]](http://s3.51cto.com/wyfs02/M00/74/2B/wKioL1YWcYmwGHk1AAIidw14Jz0252.jpg)
![clip_image033[4] clip_image033[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcXGgGmBeAAGey4xC3wg750.jpg)
![clip_image034[4] clip_image034[4]](http://s3.51cto.com/wyfs02/M01/74/2E/wKiom1YWcXGAkP_4AAHJxXu0V7M091.jpg)
![clip_image035[4] clip_image035[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcXLCfjeeAAGCoYYJAqs959.jpg)
![clip_image035[5] clip_image035[5]](http://s3.51cto.com/wyfs02/M02/74/2B/wKioL1YWcYmS2m3DAAGCoYYJAqs369.jpg)
![clip_image036[4] clip_image036[4]](http://s3.51cto.com/wyfs02/M00/74/2B/wKioL1YWcYnz7F3EAAJglBkqYDo747.jpg)
![clip_image037[4] clip_image037[4]](http://s3.51cto.com/wyfs02/M00/74/2E/wKiom1YWcXLjs96lAALTJicZTo8604.jpg)
![clip_image038[4] clip_image038[4]](http://s3.51cto.com/wyfs02/M02/74/2E/wKiom1YWcXKRW2puAAZRT7KnwBY078.jpg)